|
|
|
|
Threat Intelligence Newsletter
|
|
|
|
|
|
Welcome to the September 2024 edition of the LevelBlue Labs Threat Intelligence newsletter!
LevelBlue Labs is the threat intelligence unit of LevelBlue. LevelBlue Labs includes a global team of threat researchers and data scientists who, combined with proprietary technology in analytics and machine learning (ML), analyze one of the largest and most diverse collections of threat data in the world. Our research team delivers tactical threat intelligence that powers resilient threat detection and response — even as technology evolves, and adversaries change their tactics, techniques, and procedures.
In the Threat Intelligence Newsletter, you will find the most important threat news from the last month, recent updates to USM Anywhere detections, new pulses in OTX, and more.
|
|
|
|
|
|
Latest Threat Intelligence News
|
|
|
|
|
|
APT42: Phishing campaigns against Israel and U.S.
During the month of August, Meta, Microsoft and Google have all reported phishing attacks attributed to APT42, also known as Mint Sandstorm, during the past months. The Iranian threat actor has reportedly been targeting political and diplomatic officials in Israel and the U.S., including some associated with administrations of President Biden and former President Trump. As reported by Microsoft, this activity points as a potential attempt by Iran to influence in this year's US presidential election.
The accounts used for the phishing posted as technical support for AOL, Google, Yahoo and Microsoft, while the contents suggest the sites are using AI-enabled services to plagiarize at least some of their content from US publications. Furthermore, the Trump campaign claims it was hacked by Iran after a trove of sensitive documents were leaked to Politico at the end of July.
|
LevelBlue Labs latest blog: SbaProxy
LevelBlue Labs has identified in its latest blog a new malware, named SbaProxy, found masquerading as legitimate anti-virus components to establish proxy connections through a command and control (C&C) server. This tool, distributed in various formats such as DLLs, EXEs, and PowerShell scripts, is challenging to detect due to its sophisticated design and legitimate appearance.
By modifying legitimate anti-virus binaries and using valid certificates, the threat actors have made SbaProxy particularly stealthy. This threat has a significant impact, as it can be used to create proxy services that facilitate malicious activities and potentially be sold for financial gain.
|
Jenkins RCE vulnerability exploited in the wild
CISA has included a critical Jenkins vulnerability (CVE-2024-23897) in its catalog of Known Exploited Vulnerabilities (KEV). Jenkins is a popular open-source automation server that assists developers in automating the software development process.
The exploitation in the wild reportedly began in March. According to CloudSEK, the threat actor IntelBroker had leveraged this vulnerability to compromise the IT service provider BORN Group, gaining access to many of theirs customers, such as Reebok, Ireland Bank, Nestle or Hitachi.
Additionally, Juniper Networks reported that the RansomEXX group exploited this vulnerability to infiltrate the systems of Brontoo Technology Solutions, a provider of technology services to Indian banks, in late July. This ransomware attack led to significant disruptions in retail payment systems across the country.
|
|
|
|
|
|
Tracking, Detection & Hunting Capabilities
|
|
|
|
|
|
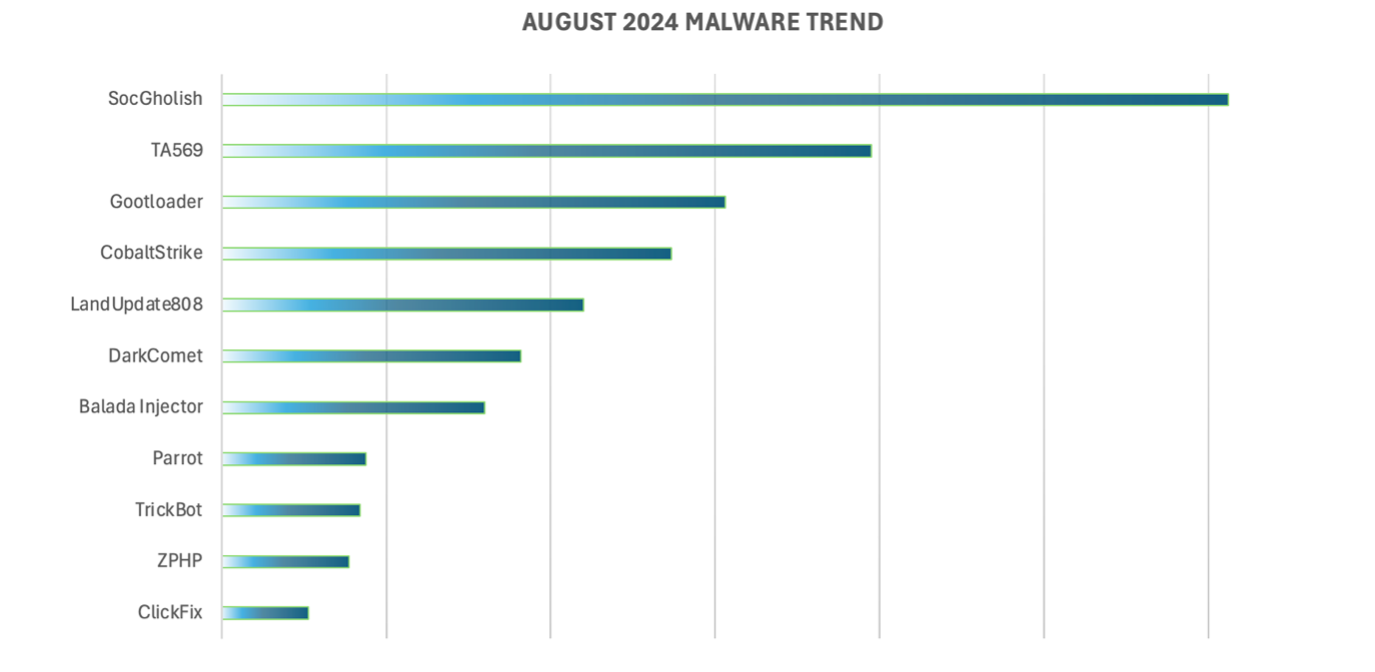
The team has identified the following malware/threat actors as the most active during the month of August. August’s malware trends continue to be very similar to previous months, with a main relevant inclusion:
|
- LandUpdate808: This fake update variant was initially reported on early July by the Hawaian guys in Malasada Tech. Since their initial report, it has become a popular malware family in July and August LevelBlue’s dashboards due to its use of compromised domains to deliver their payloads. The events containing these domains are often challenging to pan between benign/malicious since they don’t always carry the full URL. This same hurdle has occurred with SocGholish during the past months, maintaining it in the top of the list.
|
|
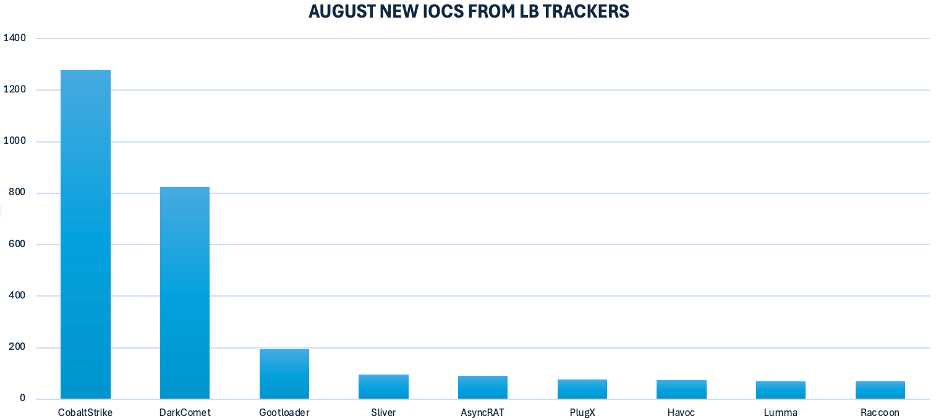
The LevelBlue trackers have identified over 3300 new IOCs for the different families it tracks. The busiest trackers during the month of August have been:
|
|
USM Anywhere Detection Improvements
In August, 88 USM Anywhere detections were added or improved. Here are a few examples of improvements and new elements created:
|
- Created several new rules related to Anomalous User Behavior for Microsoft O365, Okta and targeted phishing campaigns and more.
- Enhanced OTX Indicators of Compromise rules to break them down into specific methods, including Custom Subscriptions and ACSC feeds.
- Improved several rules from Vectra IA.
|
Please visit the LevelBlue Success Center for a full list of improvements, new elements, issues found, and tasks created.
|
LevelBlue Labs Open Threat Exchange
LevelBlue Labs Open Threat Exchange (OTX) is the world’s largest open threat intelligence community, made up of 450K threat researchers who publish threat information from 140 different countries on the OTX platform, which our LevelBlue Labs team enriches and consumes.
You can go here to find out more about the new pulses or to sign up to be part of the community.
|
New OTX Pulses
The LevelBlue Labs team is continuously creating new Pulses in OTX based on what they are seeing in the wild. In August, 96 new Pulses were created by the Labs team, providing coverage for the latest threats and campaigns. Here are a few examples of the most relevant new Pulses:
|
- Iran-based Cyber Actors Enabling Ransomware Attacks on US Organizations
- BORN Group Supply Chain Breach: In-Depth Analysis of Jenkins Exploitation
- Increased Activity Against Apache OFBiz CVE-2024-32113
- Botnet 7777: Are You Betting on a Compromised Router?
|
|
|
|
|
|
To have Release Notes emailed to you automatically, follow these steps:
|
2. Click on the announcement for the product you wish to follow.
3. Select the “Follow” button on the right-hand side.
4. Select the drop-down menu on the right-hand side and choose “Every Post” to enable receiving emails from leading security and IT tools.
|
|
|
|
|